In an era where data breaches make headlines and regulatory fines reach into the billions, understanding data sovereignty has become essential for IT leaders. Whether you’re an IT administrator evaluating secure file sharing solutions or a CTO navigating complex compliance requirements, data sovereignty affects how you store, process, and protect your organization’s most valuable asset: its data.

FileCloud’s content model places data (and storage) at the center of an Enterprise Content Management framework, with overlapping layers for metadata, access control, governance, data leak prevention, compliance, and digital rights management. These layers support data sovereignty.
What is Data Sovereignty?
Data sovereignty is the principle that digital information is subject to the laws and regulations of the country where it is stored. While your organization may own the data, its handling and protection must comply with the legal framework of the hosting jurisdiction.
This isn’t just a technical consideration—it’s a legal one. When you store data in a particular country, that data falls under that nation’s governance structures, privacy laws, and regulatory oversight. For organizations operating globally, this creates a complex web of obligations that can vary dramatically across borders.
Why Data Sovereignty Compliance Matters More Than Ever
The importance of data sovereignty has intensified as data has become the currency of the modern economy. Here’s why it should be on every IT leader’s radar:
-
Regulatory Compliance is Non-Negotiable
Data protection regulations like GDPR in the European Union, HIPAA in the United States, and the Kingdom of Saudi Arabia’s Personal Data Protection Law (PDPL) often require that certain types of data remain within specific legal jurisdictions (referred to as a data residency requirement). Failure to comply with data sovereignty laws can result in substantial legal consequences, hefty fines, and lasting damage to your organization’s reputation.
For IT administrators responsible for implementing compliant solutions, this means carefully evaluating where data centers are located and understanding which jurisdictions govern your data. For C-suite executives, non-compliance represents a significant financial and reputational risk that can’t be ignored.

-
Privacy Protection and Legal Accountability
Data sovereignty ensures that personal and sensitive information is governed by your country’s laws—not foreign jurisdictions. This is crucial for safeguarding privacy rights and preventing unauthorized access, surveillance, or misuse of sensitive data.
When data crosses borders, it may become subject to foreign government access requests or surveillance programs that conflict with your organization’s privacy commitments. Maintaining data sovereignty means maintaining control over who can access your data and under what circumstances.
-
Security Standards Vary Globally
Different countries maintain varying cybersecurity standards and data protection requirements. Ensuring data sovereignty can be challenging when attempting to maintain consistent and robust security measures across different locations. International or cross-border data transfers and foreign hosting can expose data to security gaps that wouldn’t exist with sovereign storage solutions.
-
National Security and Business Interests
Governments often have legitimate concerns about the security of their citizens’ data, especially when it comes to classified or sensitive information. Data sovereignty allows governments to maintain control over such data to safeguard national security.
For enterprises, data sovereignty protects intellectual property and proprietary information from foreign access. This is particularly critical for organizations in regulated industries or those handling government contracts.
Data Sovereignty Requirements
Meeting data sovereignty obligations requires understanding both the specific regulations that apply to your organization and the technical controls needed to maintain compliance.
Organizations operating across multiple regions often find themselves managing a patchwork of requirements: European data under GDPR must generally remain within the EU or approved jurisdictions, while countries like China, Russia, and India have implemented data localization laws requiring certain data types to remain within their borders.
The key for IT leaders is to map your data inventory against applicable regulations, identify which datasets have sovereignty requirements, and then architect your infrastructure and select vendors that can support these geographically-specific compliance needs.
Data Visibility
At a fundamental level, data sovereignty requirements typically mandate that certain categories of data—personal information, financial records, healthcare data, or government information—must be not only be stored but also processed and managed within specific geographic boundaries (referred to as data localization).
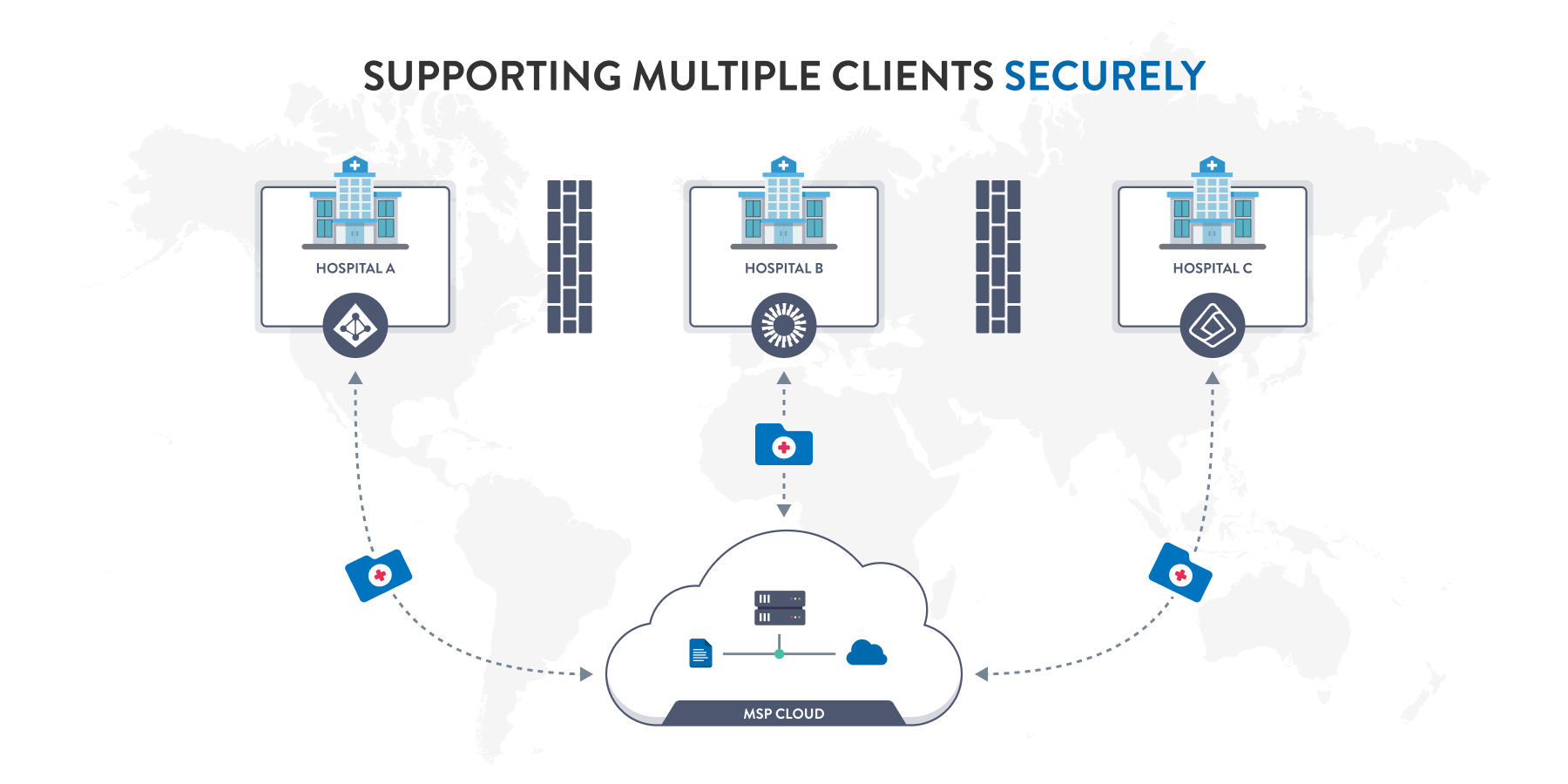
Data localization requirements are particularly relevant for Managed Service Providers that support IT infrastructure and data storage for clients in highly regulated industries (such as healthcare) headquartered in different countries.
Infrastructure Clarity
For IT administrators, this translates into concrete technical requirements: knowing the physical location of every data center where your information resides, ensuring backup and disaster recovery systems also comply with jurisdictional requirements, and maintaining detailed documentation of data flows and storage locations.
Access Controls
Additionally, many regulations require that data sovereignty extends beyond just storage—it also encompasses data protection frameworks and access controls. It’s not a simple matter of securing and authenticating end-user access; data sovereignty requirements may stipulate that administrative access and support personnel be located within the same jurisdiction.
Data Sovereignty in Cloud Environments
The rise of cloud computing has complicated data sovereignty considerably. When organizations store data in the cloud, it may be physically located in data centers across different countries or regions, each with its own set of laws governing data privacy, security, and access.
The Sovereign Cloud Challenge
Implementing a sovereign cloud strategy requires careful consideration of several factors:
- Legal Jurisdiction: Cloud data may reside in multiple locations simultaneously, making it essential to understand which laws apply and how they interact with your compliance obligations.
- Data Control: Data sovereignty affects your organization’s control over its data. You need to carefully choose where to store data to comply with relevant laws while retaining control over who can access and manage it.
- Hybrid and Multi-Cloud Solutions: Many organizations address data sovereignty concerns through hybrid or multi-cloud approaches, storing sensitive data in specific sovereign locations while using public cloud services for non-sensitive workloads.

Key Data Sovereignty Challenges
Navigating data sovereignty requirements presents several challenges for IT organizations:
- Varying Regulations: Different countries maintain vastly different data protection laws and regulations. Ensuring compliance across multiple jurisdictions can be complex and costly.
- Cross-Border Data Transfers: Transferring data across borders may require specific agreements or mechanisms, such as Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs), to ensure data remains protected.
- Operational Impact: Data sovereignty requirements can impact the scalability and efficiency of global business operations, as organizations navigate complex regulatory landscapes while maintaining performance.
- Evolving Regulations: Data sovereignty regulations constantly evolve. Staying compliant requires ongoing monitoring and adaptation to new laws.
Implementing Secure Sovereign File Sharing
For IT administrators tasked with implementing secure sharing while maintaining file sovereignty, several strategies prove effective:
- Choose the Right Infrastructure: Select file sharing solutions that support on-premises deployment, hybrid configurations, or region-specific hosting to maintain compliance with data sovereignty requirements.
- Implement End-to-End Encryption: Ensure that data is encrypted both in transit and at rest, providing strong protection against unauthorized access regardless of where it’s temporarily processed.
- Establish Access Controls: Utilize robust access controls and permissions to restrict who can access and modify shared files. Implement two-factor authentication and regularly review permissions.
- Monitor Data Flows: Regularly audit and monitor who accesses shared files and for what purpose. This helps identify unauthorized activities and demonstrates compliance during audits.
- Understand Data Center Locations: Work with sovereign file sharing services that allow you to specify data center locations, ensuring data remains within required jurisdictions.
- Develop Clear Policies: Create and enforce data retention policies that ensure information is deleted after its intended purpose is fulfilled and implement procedures for secure file destruction.
Moving Forward with Data Sovereignty
As data protection regulations tighten globally and cyber threats evolve, data sovereignty will only become more critical. For IT leaders, the path forward requires balancing compliance obligations with operational efficiency, security requirements with user experience, and local control with global collaboration.
The organizations that succeed will be those that treat data sovereignty not as a checkbox exercise but as a fundamental component of their data protection strategy. By understanding the legal landscape, implementing appropriate technical controls, and choosing solutions designed for sovereign storage and file sharing, IT leaders can protect their organizations while enabling secure collaboration in an increasingly connected world.
Whether you’re evaluating new file sharing platforms, redesigning your cloud architecture, or developing policies for international data transfers, data sovereignty must be central to your decision-making. The stakes—regulatory compliance, data security, privacy protection, and business continuity—are simply too high to treat it as an afterthought.
Interested in learning how FileCloud can support sovereign file sharing for your organization? Sign up for a free trial or schedule a personalized demo.


Product Marketing Manager