As social and economic activities continue their migration online, data protection and privacy have evolved from IT considerations to fundamental business requirements. According to the United Nations Conference on Trade and Development (UNCTAD), 79% of countries worldwide now have data protection and privacy legislation in place—a dramatic increase that reflects growing global recognition of data sovereignty as a critical governance issue.
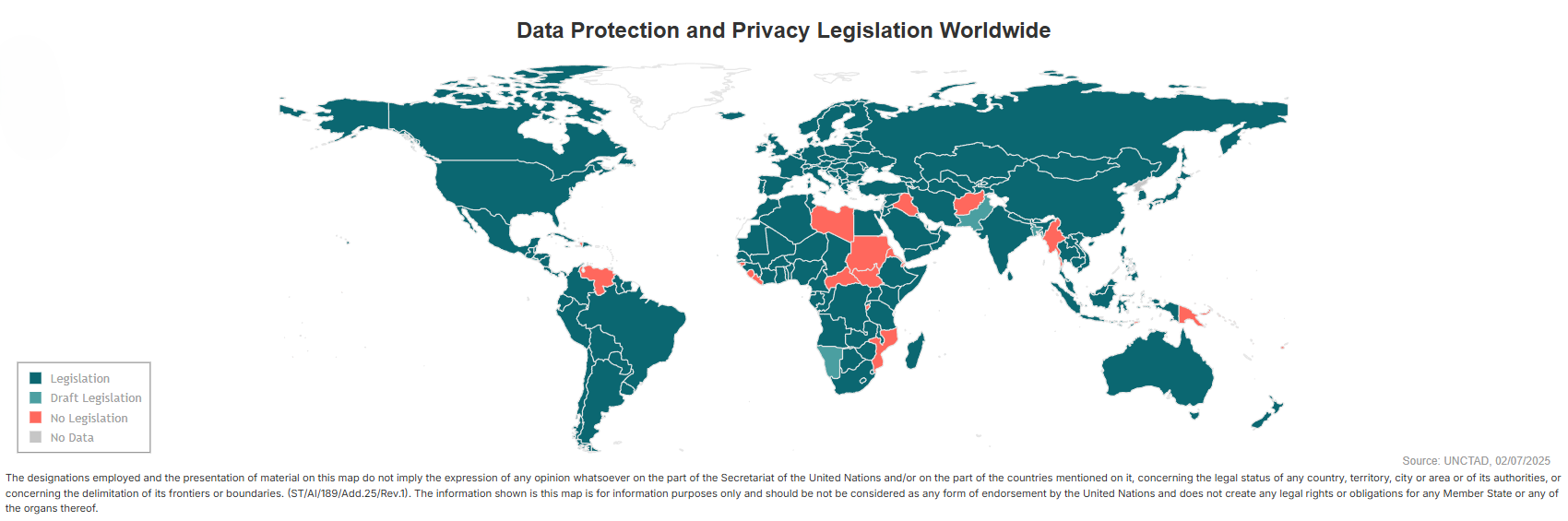
Image Source: UNCTAD, Data protection and privacy legislation worldwide
The implications for enterprise IT leaders are significant. Organizations operating across borders or within highly regulated industries must navigate an increasingly complex landscape of compliance requirements. From GDPR in the European Economic Area to Saudi Arabia’s PDPL, from CCPA in California to NIST 800-171 and CMMC requirements for U.S. defense contractors, data sovereignty regulations demand that enterprises maintain precise control over where data resides, how it’s encrypted, and who can access it.
This regulatory environment makes Enterprise File Sync and Share (EFSS) vendor selection a strategic decision rather than a simple technology procurement. The right platform must balance security, compliance, usability, and cost while adapting to your organization’s specific regulatory obligations and infrastructure requirements.
This guide provides a vendor-neutral comparison of leading EFSS solutions designed for data sovereignty compliance. We’ll examine seven platforms—FileCloud, Kiteworks, Box, Egnyte, ShareFile, ownCloud, and Nextcloud—across the dimensions that matter most for compliance-driven deployments.
Key Evaluation Criteria When Selecting a Vendor for Data Sovereignty
Before diving into individual vendors, let’s establish the critical capabilities that enable data sovereignty compliance:
- Deployment Flexibility: Can you deploy on-premises, in specific cloud regions, or in hybrid configurations that meet data residency requirements?
- Encryption Standards: Does the platform support FIPS 140-2 validated encryption for organizations handling controlled unclassified information (CUI) or working with government agencies?
- Compliance Frameworks: Are there built-in dashboards, configurations, or guidance for regulations like GDPR, HIPAA, NIST 800-171, ITAR, or CMMC?
- Data Governance: Can you implement automated classification, metadata management, data loss prevention (DLP), and retention policies?
- Audit Capabilities: Does the platform provide comprehensive logging and reporting to demonstrate compliance during audits?
- Administrative Control: Can IT teams maintain centralized visibility and granular access controls across all deployment models?
File Sharing Vendor Comparisons
FileCloud
Deployment Options: Cloud, on-premises, and hybrid with transparent pricing across all models. Supports data residency requirements even for cloud deployments, with regional deployment options.
Compliance & Security: FIPS 140-2 validated encryption available through FIPS mode. Comprehensive Compliance Center with configurations for GDPR, HIPAA, NIST 800-171, ITAR, and KSA PDPL. Built-in DLP and digital rights management (DRM) without third-party integrations.
Data Governance: Robust metadata management with custom and built-in tags. Smart content classification with visual and RegEx builders for automated tagging. Hierarchical retention policies across multiple levels (Admin, Legal Hold, Retention, Trash, Archival).
Key Strengths: Full-featured admin dashboard at base tier. Unlimited file versioning and file size uploads. Native workflow automation and e-signature integration. Comprehensive audit logs and reporting without tier restrictions.
Best For: Organizations requiring flexible deployment with strong built-in compliance features. Particularly suitable for defense contractors, government agencies, healthcare organizations, and financial services firms needing FIPS validation or multi-framework compliance.
Kiteworks
Deployment Options: On-premises and cloud deployment available (restricted to Enterprise tier).
Compliance & Security: Offers compliance features and security capabilities, but certain advanced functions may require Enterprise tier or specific add-ons. DLP and DRM available through separate SafeEDIT add-on. Content classification available with Advanced Governance add-on.
Data Governance: Content classification available but without visual or RegEx builders for rule creation. Other governance features spread across licensing tiers and add-on packages.
Key Strengths: Established presence in highly regulated industries. Comprehensive security certifications.
Considerations: Tier-based and add-on model can significantly increase total cost of ownership. Advanced features often require multiple upgrades or separate packages.
Best For: Large enterprises with budget for premium tiers who prioritize established vendor reputation in regulated markets.
Box
Deployment Options: Cloud-only SaaS solution. No on-premises or hybrid deployment options, which limits flexibility for data residency requirements.
Compliance & Security: Strong security certifications and enterprise-grade features, but many governance capabilities restricted to Business Plus, Enterprise, or Enterprise Plus tiers. RBAC, data residency controls, and enterprise admin console require tier upgrades.
Data Governance: Some DLP capabilities available, but advanced governance features spread across multiple premium tiers. File versioning unlimited only at Enterprise Plus or higher.
Key Strengths: Established cloud platform with extensive third-party integrations. User-friendly interface. Strong market presence.
Considerations: Tier-based restrictions on critical compliance features. 5GB file size limits at business tiers. External account management requires Business Plus or higher.
Best For: Organizations comfortable with cloud-only deployment and budget for premium tiers to access governance features.
Egnyte
Deployment Options: Cloud-focused with hybrid capabilities through file synchronization with Windows servers. No true on-premises option for organizations requiring self-hosted infrastructure.
Compliance & Security: Ransomware protection and endpoint backup available as add-ons or in higher enterprise tiers. SSO/SAML and 2FA for external accounts require additional add-on purchases, driving up costs.
Data Governance: Full audit trail and reporting capabilities available, but DLP, retention policies, and classification features restricted to Ultimate tier (several upgrades from base tier).
Key Strengths: Hybrid synchronization capabilities. Cloud infrastructure with regional options.
Considerations: No FIPS 140-2 validation. Limited file versioning at business tier. 100GB file size limit without resumable uploads.
Best For: Organizations prioritizing cloud deployment with some hybrid capabilities and willing to invest in Ultimate tier for comprehensive governance.
ShareFile
Deployment Options: Primarily cloud-focused. Offers “Storage Zones” for hosted, private cloud, or on-premises storage, but pricing and implementation details not publicly available, complicating procurement and comparison processes.
Compliance & Security: Provides encryption for data at rest and in transit, but lacks FIPS-validated encryption—a potential deal-breaker for government agencies, defense contractors, and organizations in highly regulated industries requiring validated cryptographic standards.
Data Governance: Comprehensive audit logs available only with Virtual Data Room plan upgrade. DLP available only through third-party integration, requiring additional procurement, integration, and testing. Limited built-in metadata capabilities (title, size, creator, upload date) compared to more robust enterprise solutions.
Key Strengths: Suitable for specific workflows and business use cases. Established presence in document-centric industries with straightforward sharing requirements.
Considerations: Missing native DLP functionality requires additional vendor relationships and integration complexity. Compliance gaps in audit logging and governance tools may complicate regulatory demonstrations during audits. 100GB upload limit without resumable uploads can impact productivity for teams working with large files.
Best For: Organizations with relatively straightforward compliance requirements and workflows centered on document sharing rather than complex governance needs.
ownCloud
Deployment Options: On-premises and cloud deployment capabilities, but following Kiteworks acquisition, pricing information no longer publicly available. DIY configuration process requires extensive technical expertise.
Compliance & Security: Encryption available but not FIPS-validated. Advanced security features like SAML SSO and ransomware protection restricted to expensive enterprise plans, creating security gaps.
Data Governance: Lacks FIPS-validated encryption and integrated compliance dashboards. Limited governance framework compared to purpose-built enterprise solutions.
Key Strengths: Open-source heritage with self-hosting capabilities. Active community support.
Considerations: Performance challenges reported for large-scale enterprise deployments. Post-acquisition uncertainty around development roadmap. Limited native compliance tools.
Best For: Organizations with technical resources to manage deployment and comfortable with open-source platforms for less stringent compliance requirements.
Nextcloud
Deployment Options: On-premises only—no cloud or hybrid options. This limitation restricts infrastructure flexibility for organizations seeking hybrid approaches or cloud-based data residency options.
Compliance & Security: No FIPS 140-2 validated encryption. No integrated ransomware protection or CDR. Key security features like advanced SSO and enhanced audit logging restricted to Enterprise Premium or Ultimate tiers.
Data Governance: Basic retention policies and simplified HIPAA/GDPR configurations available, but lacks comprehensive compliance frameworks and automated management tools even at premium tiers.
Key Strengths: Open-source platform with strong privacy focus. Active development community. Full on-premises control.
Considerations: Deployment inflexibility. No workflow automation or integrated e-signature solution. Advanced collaboration features require Enterprise Premium upgrades.
Best For: Organizations requiring exclusively on-premises deployment with technical expertise to implement and manage the platform.
Vendor Overview
| Vendor |
Key Strengths |
Considerations |
Best For |
| FileCloud |
- FIPS 140-2 validated encryption
- Built-in compliance dashboards (GDPR, HIPAA, NIST, ITAR, PDPL)
- Native DLP & DRM
- Unlimited file sizes & versioning
- Transparent pricing across all deployments
|
- More features than simple use cases may require
- Smaller market presence vs. legacy vendors
|
- Government/defense contractors
- Healthcare (HIPAA)
- Financial services
- Multi-framework compliance
- Organizations needing flexible deployment
|
| Kiteworks |
- Established in regulated industries
- Comprehensive security certifications
- Strong enterprise reputation
|
- Tier-based model increases costs significantly
- Advanced features require multiple upgrades
- Deployment flexibility at Enterprise tier
- DLP/DRM (separate add-ons)
|
- Large enterprises with premium budgets
- Organizations prioritizing vendor reputation
- Existing Kiteworks users
|
| Box |
- Established cloud platform
- Extensive third-party integrations
- User-friendly interface
- Strong market presence
|
- Cloud-only (no on-premises/hybrid)
- Critical compliance features tier-restricted
- 5GB file limits at business tiers
- Unlimited versioning at Enterprise Plus+
|
- Cloud-only comfortable organizations
- Premium tier budgets
- Teams prioritizing integrations
- User-friendly collaboration needs
|
| Egnyte |
- Hybrid synchronization
- Cloud infrastructure with regional options
- Strong collaboration features
|
- No true on-premises option
- No FIPS 140-2 validation
- SSO/2FA require add-on purchases
- DLP/classification only at Ultimate tier
- 100GB file limit, no resumable uploads
|
- Cloud + hybrid deployment
- Ultimate tier investment willingness
- Add-on model acceptance
|
| ShareFile |
- Suitable for specific workflows
- Document-centric industries
- Straightforward sharing
|
- No FIPS-validated encryption
- DLP via third-party only
- Audit logs only with VDR plan upgrade
- Limited metadata
- 100GB upload limit
|
- Straightforward compliance requirements
- Document sharing focus (not complex governance)
- Simple virtual data room needs
|
| ownCloud |
- Open-source with self-hosting
- Active community support
- On-premises & cloud deployment
- Full infrastructure control
|
- Post-acquisition pricing unclear
- DIY configuration requires expertise
- Large-scale performance challenges
- No FIPS validation
- Limited native compliance tools
|
- Technical deployment resources available
- Open-source platform preference
- Less stringent compliance requirements
- Self-hosting priority
|
| Nextcloud |
- Open-source with privacy focus
- Active development community
- Full on-premises control
- European data privacy alignment
|
- On-premises only (no cloud/hybrid)
- No FIPS 140-2 validation
- No ransomware protection/CDR
- Advanced features at Premium+ tiers
- No workflow automation or e-signature
|
- Exclusively on-premises deployment
- Technical implementation expertise
- Open-source cloud priority
|
Making the Right Choice When Selecting a File Sharing Vendor for Data Sovereignty
Selecting an EFSS platform for data sovereignty compliance requires balancing multiple factors specific to your organization’s requirements:
Regulatory Requirements: Organizations subject to NIST 800-171 or CMMC requirements should prioritize vendors offering FIPS validated encryption. Those operating under GDPR, HIPAA, or ITAR need platforms with built-in compliance frameworks rather than cobbled-together third-party solutions.
Infrastructure Strategy: If maintaining on-premises infrastructure is non-negotiable, eliminate cloud-only options immediately. Organizations pursuing hybrid strategies should evaluate how seamlessly vendors support multi-environment deployments.
Total Cost of Ownership: Look beyond base pricing to understand where critical compliance features sit in vendor tier structures. Platforms requiring multiple tier upgrades or add-on purchases for essential governance capabilities may cost significantly more than transparent alternatives.
Administrative Resources: Consider your IT team’s capacity to manage complex integrations, DIY configurations, or multiple third-party tools versus unified platforms with centralized administration.
Scalability: Evaluate whether the platform can grow with your organization without forcing architectural changes or expensive migrations as compliance requirements evolve.
How to Choose the Right File Sharing Solution
Data sovereignty compliance has moved from a niche concern to a fundamental enterprise requirement. The EFSS platform you select today will shape your organization’s ability to meet current compliance obligations and adapt to future regulatory changes.
Vendors offering flexible deployment, encryption, built-in compliance frameworks, and comprehensive data governance without tier restrictions provide the strongest foundation for long-term success.
As you evaluate these platforms, prioritize vendors that align with your specific regulatory requirements, infrastructure strategy, and administrative capabilities. The right choice eliminates compliance gaps, reduces total cost of ownership, and enables your organization to focus on core business objectives rather than perpetual platform management.
For technical evaluations, we recommend requesting demos that specifically test your compliance use cases, examining how each platform handles your actual data classification requirements, and validating that audit trails meet your regulatory standards before making final vendor selections.
File Sharing Vendors for Data Sovereignty FAQs
How do file sharing vendors support data residency requirements?
Vendors may offer region-specific data centers, customer-controlled storage locations, or self-hosted and private cloud deployment options to ensure data remains within specific jurisdictions.
What regulations influence data sovereignty in 2026?
Common regulations include GDPR, HIPAA, CJIS, ITAR, FedRAMP, and emerging regional privacy laws. These rules dictate where data can be stored, how it’s accessed, and how it must be protected.
What is the difference between data residency and data sovereignty?
Data residency refers to where data is physically stored, while data sovereignty encompasses both location and the legal authority governing that data, including access rights and jurisdictional control.
Are cloud-based file sharing platforms compliant with data sovereignty laws?
Some cloud platforms are compliant, but not all. Compliance depends on factors such as data center locations, encryption, access controls, and whether customers can choose or restrict where data is stored.
Can organizations fully control their data with SaaS file sharing solutions?
Control varies by vendor. Some SaaS solutions limit infrastructure visibility, while others offer customer-managed encryption keys, audit logs, and configurable data location controls.
What industries require strict data sovereignty compliance?
Industries such as government, healthcare, finance, legal, defense, and education often have strict data sovereignty and data residency requirements due to sensitive or regulated information.
How does self-hosted file sharing improve data sovereignty?
Self-hosted solutions allow organizations to store data on-premises or in a private cloud, giving full control over data location, access, and compliance with regional regulations.

Product Marketing Manager