Post updated January 13, 2026
ITAR Compliance for File Sharing & Management with FileCloud
ITAR provides a set of government regulations dictating how to prevent the distribution of defense items and services outside the US. ITAR compliance makes it compulsory for companies to monitor and control inbound and outbound network traffic. FileCloud not only provides high security but also provides audit logs to see who accessed the cloud and for what purpose. Build a robust ITAR compliant document management and access control solution with FileCloud.
If a company fails to comply with the ITAR, it can face civil and criminal penalties. FileCloud Server is a powerful file sharing solution that provides tools for security, encryption, document management, data leak prevention, content classification, and private file sharing required to fulfill cybersecurity requirements for ITAR compliance.
FileCloud Supports ITAR Compliant File Sharing
FileCloud for ITAR is a hyper-secure, on-premises file management platform that offers file storage, access, and data governance. Custom-tailored specifically for organizations that deal with ITAR and EAR regulated data, FileCloud offers multi-layered data security, governance, and advanced record-keeping capabilities to address cybersecurity components of ITAR requirements:
- ‘End-to-End’ Encryption
- Data Classification
- Data Leak Prevention (DLP)
- Controlled Access to Data
- Security Policies & Training
FIPS 140-2 Encryption
FileCloud can be run in FIPS mode, a specific license that enforces FIPS 140-2 compliant encryption for files stored at rest and in transit.

Watermarked Previews
Admins can enable custom watermarks for shared files in the preview pane, identifying who (user) has accessed the file. Other metadata that can be configured as part of a watermark includes IP address, date stamps, and means of access.
Secure Private Access
Admins can also remove public access or shares of files, ensuring no unauthorized personnel or software can access sensitive or confidential documents. FileCloud offers private-only, time-limited, view-only, password-protected, and Zero Trust sharing permissions.

Robust Login Security
FileCloud can enable Two-Factor Authentication for users. The following options are available: Email based security code TOTP (Google Authenticator or similar TOTP code generators), DUO Security, SMS OTP Security Codes, and SMS OTP Security Codes for specific user agents. The 2FA method can be selected by Policy Group (Settings / Policies) which enables FileCloud to use different methods of authentication for different groups of users.
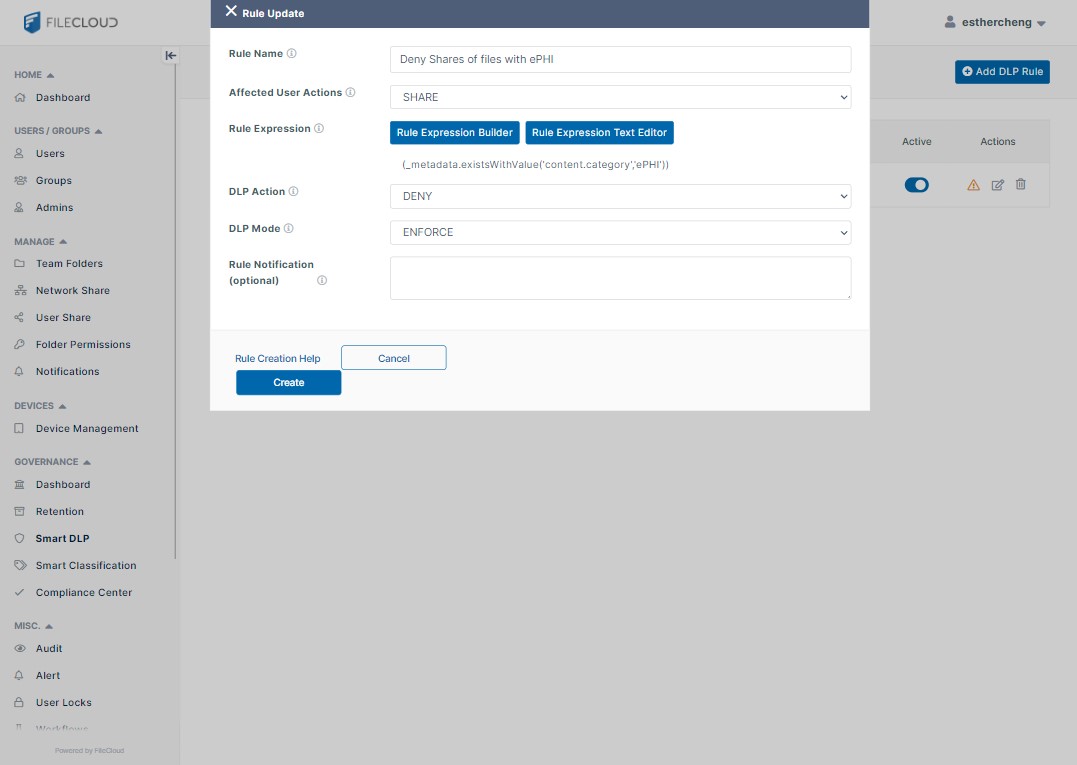
Smart Data Leak Prevention
Data leak prevention (DLP) is facilitated in FileCloud through a rules-verification system that enables administrators to closely control the degree to which users can access, edit, download, and transfer their organization’s files and folders. While DLP rules can be useful for many different kinds of data, it can be especially critical for the secure handling of Personal Identification Information (PII) and Confidential Unclassified Information (CUI).
Record-Keeping
The ITAR requires that records be maintained for five years from the expiration of the export license or other approval. In the case of an export license exemption, this would be from the date of the transaction. FileCloud for ITAR offers complete content lifecycle management with flexible retention and archival schedules to meet ITAR record-keeping requirement
Audit Controls
All FileCloud activity is recorded in unchangeable audit logs, which can be viewed and exported from the Settings / Audit section.
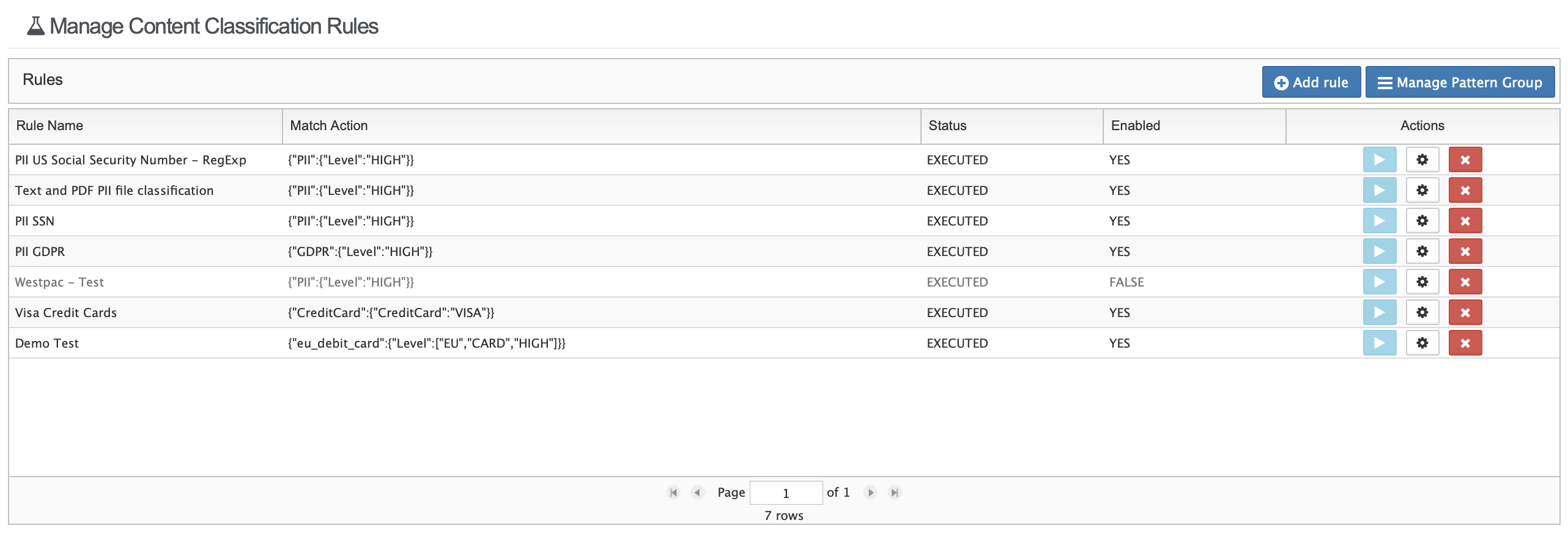
Smart Content Classification
The Content Classification Engine (CCE) is a rule-driven content classification system that enables the generic labeling of files with metadata. This labeling enables key operations within FileCloud such as contextual file search and Data Leak Prevention.
Remote Wipe
In addition to blocking a client account from accessing the environment, administrators can also prevent specific devices from logging in, as well as wipe FileCloud folders on the remote device. If the client is connected, the block and remote wipe will occur and the client will automatically log out.
Enable Password Guidelines
At any time a password is created or updated before the password is accepted, FileCloud Server checks the suggested password against the US NIST Password Guidelines list.
Streamlined ITAR Management with FileCloud Compliance Center
Managing ITAR compliance across multiple security features and settings can be complex, but FileCloud’s Compliance Center simplifies this process by consolidating all ITAR-related configurations into a single, purpose-built interface. The dedicated ITAR tab serves as a centralized command hub where administrators can monitor, configure, and maintain compliance posture in real-time. Rather than navigating through disparate settings menus, administrators can quickly verify that FIPS 140-2 encryption is active, review current DLP policies, check authentication requirements, and confirm watermarking settings—all from a single dashboard that maps directly to ITAR cybersecurity requirements.

The ITAR tab provides real-time compliance status indicators, alerting administrators to potential gaps or misconfigurations before they become violations. This proactive approach enables organizations to maintain continuous compliance rather than scrambling to prepare for audits. The interface clearly connects each FileCloud security feature—from content classification and retention policies to remote wipe capabilities and password guidelines—to its corresponding ITAR requirement, making it easier for compliance officers and IT administrators to collaborate effectively.
By streamlining ITAR compliance management into an intuitive, centralized interface, FileCloud reduces the administrative burden while strengthening security posture. Organizations can confidently demonstrate their compliance readiness with comprehensive visibility into all ITAR-relevant settings, backed by the unchangeable audit logs and robust record-keeping that regulators expect.
Hyper-secure EFSS Solution for Enterprises Subject to ITAR
FileCloud Server is a robust platform packed with compliance-supportive features and functionalities that specifically support cybersecurity requirements within the ITAR. Self-host FileCloud Server on-premises or deploy within a private cloud or as a network overlay to enable easy, remote file access and sharing while maintaining total control over data.

Interested in learning more about FileCloud for ITAR Compliance?
Register for a Free Trial | Watch On-demand Demo | Contact a Sales Engineer

By Team FileCloud