FileCloud and Signority Complete SOC 2® Type 2 Audits: What This Means for Enterprise Security
When evaluating enterprise software vendors, particularly those handling sensitive data, security audits and reporting serve as critical decision-making criteria. Both FileCloud and Signority have received SOC 2 (System and Organization Controls 2) Type 2 reports—a significant milestone that demonstrates our sustained commitment to protecting an organization’s most valuable asset: data.
This achievement represents more than a compliance checkbox. It provides independent verification that security controls operate effectively over time, offering the operational assurance that CTOs, CISOs, and compliance officers require when selecting technology partners for mission-critical deployments.
Understanding SOC 2 Type 2 Reports
SOC 2 Type 2 reports (sometimes appearing as SOC 2 Type ii reports) represent the gold standard for evaluating service organizations’ security posture. Developed by the American Institute of Certified Public Accountants (AICPA), the SOC framework provides a rigorous assessment methodology that goes far beyond surface-level security reviews.
Unlike SOC 2 Type 1 audits, which evaluate whether appropriate controls exist at a single point in time, the SOC 2 Type 2 audit examines whether those controls operated effectively throughout an extended observation period. Prescient Assurance LLC conducted comprehensive assessments for FileCloud (June 1, 2025 to October 31, 2025) and Signority (August 9, 2024 through October 31, 2025).
This temporal dimension matters. Any organization can implement security controls temporarily for an audit snapshot. Maintaining those controls consistently across months of operation—adapting to threats, managing incidents, and sustaining operational discipline—demonstrates genuine security maturity.
The Five Trust Service Criteria
The SOC 2 Type 2 report evaluates organizations against five critical Trust Service Criteria that form the foundation of comprehensive information security:
- Security addresses whether systems are protected against unauthorized access, both physical and logical. This encompasses network security, access controls, system monitoring, and incident response capabilities.
- Confidentiality examines how organizations protect information designated as confidential. This criterion proves particularly relevant for enterprises in regulated industries where data protection requirements extend beyond general security practices.
- Processing Integrity validates that systems process data completely, accurately, and in a timely manner. For content collaboration platforms, this ensures that files sync correctly, versions maintain integrity, and workflows execute as designed.
- Availability confirms that systems remain operational and accessible as committed. For organizations depending on file sharing and e-signature capabilities for business-critical operations, availability directly impacts productivity and revenue.
- Privacy addresses how organizations collect, use, retain, disclose, and dispose of personal information in conformity with privacy commitments. With evolving global privacy regulations, this criterion has become increasingly significant for multinational deployments.
Why SOC 2 Type 2 Compliance Matters for Enterprise Procurement
For organizations evaluating content collaboration and e-signature solutions (such as FileCloud and Signority), SOC 2 Type 2 compliance delivers tangible benefits that extend beyond security assurance:

Risk mitigation for regulated industries: Healthcare organizations managing HIPAA-protected information, financial institutions handling sensitive client data, and defense contractors working with controlled unclassified information require vendors who demonstrate proven security capabilities. The SOC 2 Type 2 audit provides the documented evidence these organizations need.
Streamlined vendor assessments: IT administrators and compliance officers often spend significant time conducting security assessments of potential vendors. A comprehensive SOC 2 Type 2 report reduces this burden by providing standardized, independently verified security documentation that satisfies many vendor risk assessment frameworks.
Audit support and regulatory compliance: When organizations undergo their own compliance audits—whether for industry standards, regulatory requirements, or customer commitments—they must demonstrate that third-party vendors maintain appropriate security controls. SOC 2 Type 2 reports provide the documentation auditors expect, reducing the compliance burden on internal teams.

Operational confidence: Perhaps most importantly, SOC 2 Type 2 reports provide operational confidence that security isn’t simply a marketing claim but a verified, sustained organizational capability.
FileCloud’s Multi-Layered Security Approach
FileCloud and Signority’s SOC 2 Type 2 reports complement existing certifications and compliance frameworks the platforms have been awarded, including ISO 27001:2022, ISO 9001:2015, HIPAA, GDPR, NIST, and more. The comprehensive security framework built into both FileCloud and Signority fulfill enterprise requirements for systematic information security management and operational controls.
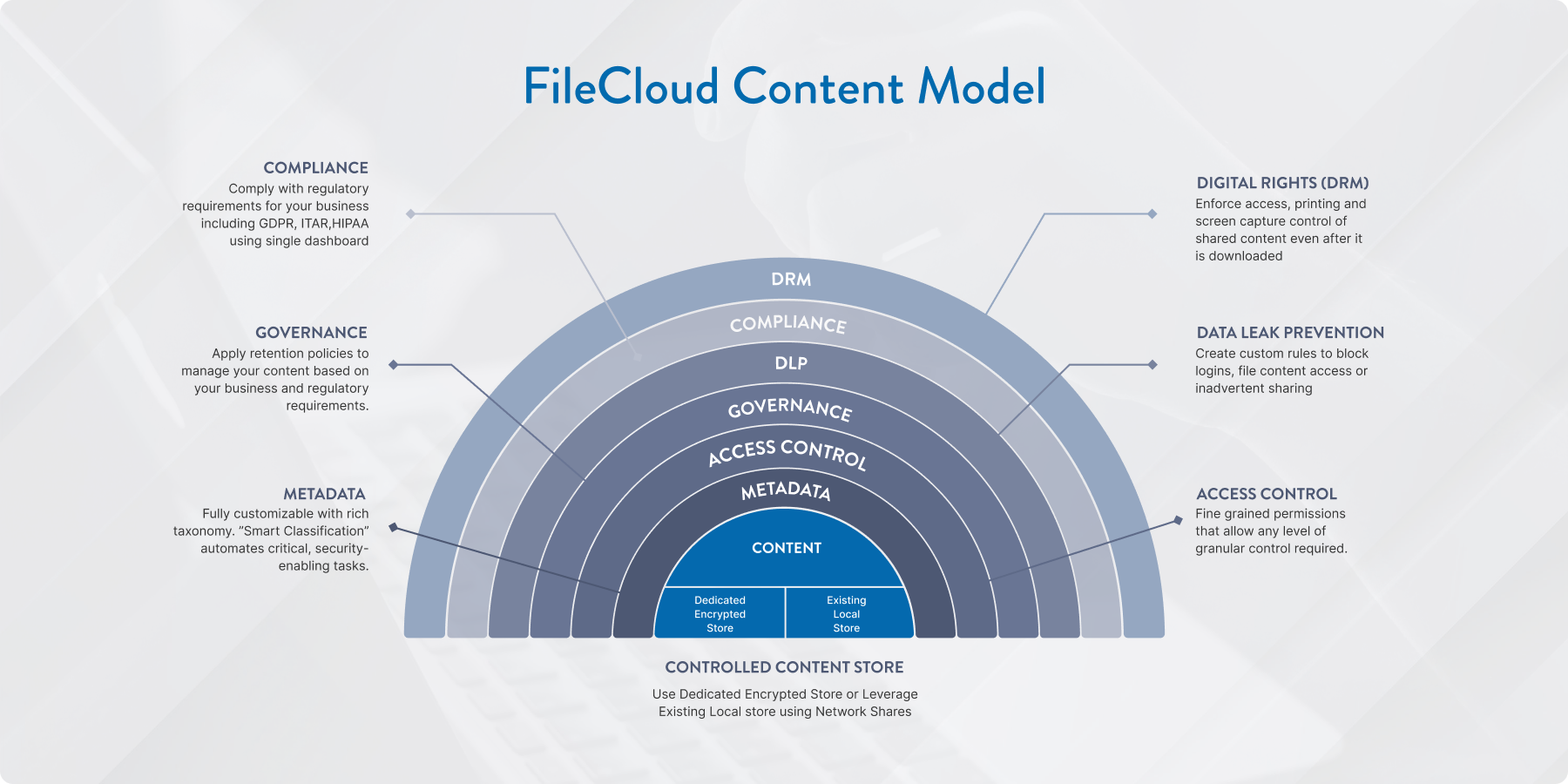
FileCloud’s content-centric security model implements protection at every architectural layer—from encrypted storage foundations and granular access controls, through metadata classification and data leak prevention, to governance policies and digital rights management that persist even after content leaves the platform. This approach ensures that security controls adapt to content sensitivity and organizational requirements rather than applying uniform protection across all data.
Similarly, Signority maintains rigorous security standards throughout the e-signature workflow, including comprehensive audit trails that provide tamper-proof documentation of every transaction, ensuring document validity and non-repudiation.
This architectural approach proves particularly valuable for organizations operating across multiple regulatory jurisdictions. The layered security controls address both systematic information security management requirements and specific operational mandates.
What This Means for FileCloud and Signority Customers
For existing and prospective customers, our SOC 2 Type 2 reports provide several immediate benefits:
- Organizations can accelerate their procurement processes by leveraging our independently verified security documentation rather than conducting extensive custom security assessments.
- IT administrators gain confidence that the platforms they deploy and manage maintain consistent security postures across ongoing operations.
- Compliance officers can satisfy audit requirements more efficiently by referencing comprehensive third-party security reports.
- C-suite executives responsible for organizational risk management can make informed decisions knowing that FileCloud and Signority have submitted to rigorous, independent security evaluations conducted according to industry-standard frameworks.
Moving Forward: Our Commitment to Security Excellence
Achieving SOC 2 Type 2 reports for both FileCloud and Signority platforms represents a significant milestone that we’re proud to mark. However, security remains a continuous journey. FileCloud maintains ongoing commitments to security excellence through regular security assessments, continuous monitoring, threat intelligence integration, and proactive control enhancements.
Our security practices don’t exist solely to satisfy compliance requirements—they’re fundamental to how we design, develop, and operate our platforms. The SOC 2 Type 2 reports simply provide independent verification of what we’ve built into our organizational DNA.
For organizations seeking content collaboration and e-signature solutions that meet the highest security standards, FileCloud and Signority now offer the documented assurance that enterprise procurement demands. Visit the FileCloud Trust Center to access our SOC 2 Type 2 reports and explore our comprehensive security documentation.
Frequently Asked Questions About SOC 2 Type 2
What is SOC 2 Type 2?
SOC 2 Type 2 is an auditing standard that evaluates how effectively a service organization’s security controls operate over an extended time period, typically six to twelve months. Unlike Type 1, which assesses controls at a single point in time, Type 2 provides assurance of sustained operational effectiveness.
What are SOC 2 Type 2 criteria?
The SOC 2 framework evaluates five Trust Service Criteria: Security (required for all audits), plus Confidentiality, Processing Integrity, Availability, and Privacy (selected based on the organization’s services and commitments). Organizations choose which criteria beyond Security apply to their operations.
Why is SOC 2 Type 2 required?
While not universally mandated by law, many enterprises require SOC 2 Type 2 reports from vendors handling sensitive data. This requirement stems from organizations’ own compliance obligations—they must ensure third-party providers maintain appropriate security controls. Additionally, industries like healthcare, finance, and government frequently establish SOC 2 Type 2 as a procurement prerequisite.
Who needs SOC 2 Type 2?
Any organization providing services that involve storing, processing, or transmitting customer data should consider a SOC 2 Type 2 audit. This particularly applies to SaaS providers, cloud service providers, data centers, and technology companies serving enterprise customers in regulated industries. For service providers, obtaining reports often represents a competitive necessity rather than an optional enhancement.

Product Marketing Manager