Data Lifecycle Management: Secure Data & Maximize Business Value
Data lifecycle management focuses on controlling data from creation through retention and secure disposal to reduce risk and operational cost. By enforcing data governance, security, and compliance at every stage, organizations protect sensitive information while increasing the long-term value and usability of their data.
In regulated and distributed environments, unmanaged data becomes both a liability and an inefficiency. A structured lifecycle approach ensures data is accessible when needed, protected at all times, and defensibly removed when no longer required.
Why Data Lifecycle Management Is Now a Business Imperative
Risk Exposure from Unmanaged Data Growth
Organizations are generating more data than ever across cloud platforms, endpoints, collaboration tools, and external portals. Without lifecycle controls, sensitive data accumulates in shared folders, personal drives, email attachments, and unmanaged repositories.
This uncontrolled sprawl increases breach exposure, insider risk, and operational blind spots. A formal lifecycle strategy reduces attack surface by applying consistent policies to all data, regardless of where it resides.
“72% of data breaches involved data stored in the cloud—30% involved data distributed across multiple environments, and incurred the highest average data breach cost at $5.05 million.”
“More than half (53%) of all breaches involve customer personal identifiable information (PII), which can include tax identification numbers, emails, phone numbers, and home addresses.”
—SecureFrame, compiled from IBM Cost of a Data Breach Report, 2024 & 2025
Rising Compliance, Audit, and Breach Pressures
Regulatory requirements such as GDPR, HIPAA, CMMC, FINRA, and regional data sovereignty mandates demand strict controls over retention, access, and data residency. Organizations must be able to demonstrate who accessed data, when it was shared, where it is stored, how long it is retained, and when and how it is deleted.
Without centralized lifecycle enforcement, compliance becomes manual, reactive, and audit intensive.
Cost and Inefficiency of Over Retained or Orphaned Data
Retaining data indefinitely increases storage costs and legal exposure. Over retention complicates eDiscovery, slows system performance, and creates redundant repositories that reduce productivity.
Lifecycle management ensures data is preserved when valuable and removed when it becomes risk without return.
The Stages of the Data Lifecycle Management
Effective lifecycle management requires structured control at every phase:
1. Data Creation and Ingestion Across Systems and Users
Data enters the organization from multiple sources including employees, vendors, clients, APIs, automated workflows, and external portals. A mature lifecycle strategy centralizes intake and ensures secure upload portals for external contributors, standardized folder structures, automated metadata tagging, and controlled ingestion into governed repositories.
Without structured ingestion, governance fails at the first step.
2. Secure Access, Collaboration, and Usage
Once data exists, it must be accessible but only to authorized users. Key requirements include granular file and folder permissions, role based access control (RBAC), secure external sharing, expiration dates on shared links, password protected or zero trust file exchanges, and remote access without VPN dependency.
Lifecycle security ensures collaboration does not compromise confidentiality.
3. Classification, Governance, and Policy Enforcement
Data must be classified and governed continuously, not just at rest. Modern lifecycle controls rely on custom metadata tagging, automated classification rules, data loss prevention enforcement, activity logs and audit trails, and policy based restrictions on sharing or download.
Classification provides the context required to apply intelligent retention, monitoring, and deletion policies.
4. Retention, Archiving, and Long Term Preservation
Retention must align with both regulatory mandates and operational needs. An effective lifecycle framework supports automated retention schedules, policy driven archiving, legal hold capabilities, tiered storage management, and enforcement based on metadata or classification.
Retention is not about keeping everything. It is about keeping what is required and defensibly managing the rest.
5. Defensible Deletion and Secure Data Disposal
Data that is no longer required becomes a liability. Secure disposal requires automated deletion triggers, audit logged erasure events, enforced policy expiration, controlled removal from user access, and verification for regulatory defensibility.
Defensible deletion reduces breach exposure and minimizes long term compliance risk.
Data Lifecycle Management Framework for End-to-End Security
A comprehensive lifecycle framework integrates security, governance, and infrastructure controls into a unified operating model.
Least Privilege Access and Zero Trust Sharing Models
Lifecycle security depends on a deny by default posture. Users should only access data required for their role. Zero Trust File Sharing® encrypts sensitive archives, prevents platform level visibility into protected content, restricts share permissions, and enables controlled external collaboration.
This minimizes lateral movement in the event of credential compromise.
Auditability, Monitoring, and Compliance Readiness
Lifecycle enforcement must be measurable. Security and compliance teams require detailed activity logs, download and access tracking, file change history, SIEM integration, and real time alerts for anomalous behavior.
Audit readiness should be built into daily operations, not assembled retroactively.
Data Residency, Encryption, and Infrastructure Control
Data sovereignty and deployment flexibility are critical for regulated industries. A secure lifecycle framework supports on-premises deployment, hybrid cloud models, region specific hosting, encryption at rest and in transit, and integration with AD, LDAP, and SSO systems.
Control over infrastructure ensures compliance with jurisdictional and industry specific mandates.
Data Lifecycle Management With FileCloud
Defining lifecycle stages is not the challenge. Enforcing them consistently across the enterprise is.
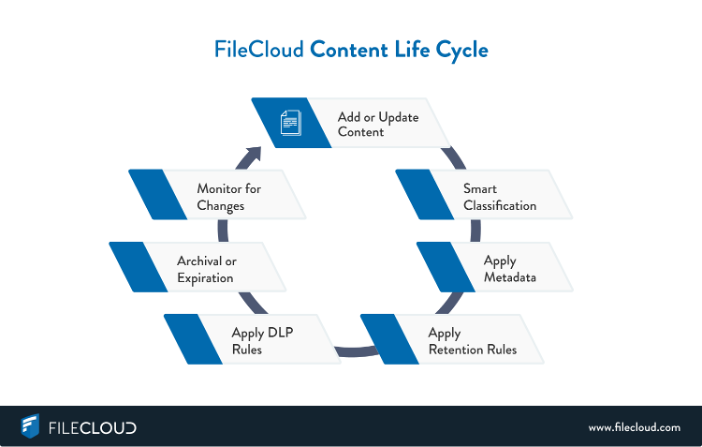
FileCloud enables enforceable data lifecycle management within a single platform. Organizations can apply granular access controls, secure external sharing, metadata driven classification, automated retention policies, and defensible deletion without relying on disconnected tools.
Custom metadata triggers governance actions such as retention schedules, DLP enforcement, workflow controls, and archival. Zero Trust file® sharing protects highly sensitive data through encrypted, password protected archives where decryption keys are not stored within the system.
With support for on-prem, hybrid, and cloud deployments, FileCloud aligns lifecycle enforcement with data residency and regulatory requirements. Built in collaboration tools, virtual drives, sync clients, and directory integration ensure security policies operate seamlessly within everyday workflows.

Product Marketing Manager