Data Loss Prevention (DLP) Strategy Steps: Guide to Building an Effective Data Loss Prevention Plan
A well-designed DLP strategy is no longer optional. As organizations expand across cloud platforms, remote work environments, and third-party ecosystems, sensitive data moves faster and farther than ever before. At the same time, stricter data sovereignty laws and cross-border data transfer regulations are placing greater pressure on organizations to maintain control over where data is stored, processed, and accessed. Without a structured data loss prevention strategy, businesses risk regulatory penalties, reputational damage, and operational disruption.
1. Define Your Data Loss Prevention Objectives and Risk Profile
Start your DLP strategy by clearly defining what sensitive data you must protect and why. Align your data loss prevention plan with regulatory requirements such as GDPR, HIPAA, or industry mandates, and tie it directly to business priorities like customer trust and operational continuity.
Next, conduct a focused security risk assessment. Identify where sensitive data is stored, who can access it, how it is shared, and where controls are weak. Pay special attention to remote access, third-party collaboration, and legacy systems.
Finally, document your primary risk scenarios. Include both insider risks such as oversharing or misconfigured permissions and external threats like phishing or ransomware. Prioritizing these risks will help you build a practical and effective DLP implementation strategy instead of a theoretical one.
2. Discover and Map Sensitive Data Across Your Environment
Gain visibility before enforcing controls. Identify where sensitive data lives across endpoints, cloud platforms, shared drives, and on-prem systems. Focus on high-risk data types such as PII, financial records, intellectual property, and healthcare information.
Map how this data moves across departments, regions, and external collaborators. Understanding data flows helps you apply DLP controls where exposure risk is highest and strengthens your overall data governance framework.
3. Implement Data Classification and Metadata Controls
Once data is identified, classify it. Create clear categories such as public, internal, confidential, and restricted. Align these classifications with your information security strategy and compliance requirements.
Use automated tagging and metadata to scale classification across large volumes of files. Apply read-only metadata where necessary to preserve audit integrity and prevent tampering. Classification should directly trigger enforcement actions such as access restrictions, retention rules, or DLP policies.
Data Sovereignty vs. Data Residency
Learn how data sovereignty differs from data residency and why the distinction is critical for regulatory compliance. Click to explore the full breakdown.
4. Establish Granular Access Controls and Least Privilege Policies
Limit access to sensitive data based on role and business need. Implement role-based access control and enforce file and folder-level permissions to reduce unnecessary exposure.
Actively review external sharing permissions and remove excessive access. Apply Zero Trust pillars so access is continuously verified and never assumed. This reduces insider risk and prevents oversharing across internal and third-party environments.
5. Deploy Endpoint DLP and Cloud DLP Protections
Extend protection across hybrid environments. Monitor file uploads, downloads, and transfers on endpoints and in cloud storage platforms.
Ensure sensitive data is encrypted at rest and in transit. Apply controls to external sharing, including expiration dates, password protection, and restricted permissions. Endpoint DLP controls should work together to protect remote and distributed workforces.
6. Enforce Retention, Archiving, and Automated Policy Workflows
Reduce risk by limiting how long sensitive data is stored. Implement automated data retention policies and deletion policies aligned with regulatory requirements.
Use automated workflows to enforce policy rules consistently. Enable temporary or transient file sharing when required, and ensure expired access is revoked automatically. Automation reduces manual oversight and strengthens compliance enforcement.

7. Enable Real-Time Monitoring, Logging, and Audit Trails
Visibility is critical to an effective DLP roll out strategy. Track user activity, file access, permission changes, and sharing behavior.
Integrate with SIEM systems to centralize alerts and correlate suspicious activity. Configure automated alerts for unusual behavior such as bulk downloads or repeated failed login attempts. Detailed audit trails help demonstrate regulatory compliance and support incident response.
8. Test, Refine, and Scale Your DLP Implementation Strategy
Start with pilot DLP projects to validate policies before full deployment. Measure outcomes such as policy violations, reduced oversharing, and improved response times.
Refine controls to balance security and usability. As your organization grows, ensure your data loss prevention project plan scales across users, departments, and geographic regions without increasing administrative complexity.

Common Challenges in DLP Implementation (and How to Avoid Them)
Many DLP initiatives fail due to overly complex tools that reduce user adoption. Choose solutions that integrate smoothly into existing workflows.
Another common issue is poor visibility into unstructured data. Invest in automated classification and discovery tools. Finally, ensure technical controls directly enforce your data protection policy. A documented policy without enforcement creates compliance gaps.
Aligning Your DLP Strategy with Zero Trust Security Principles
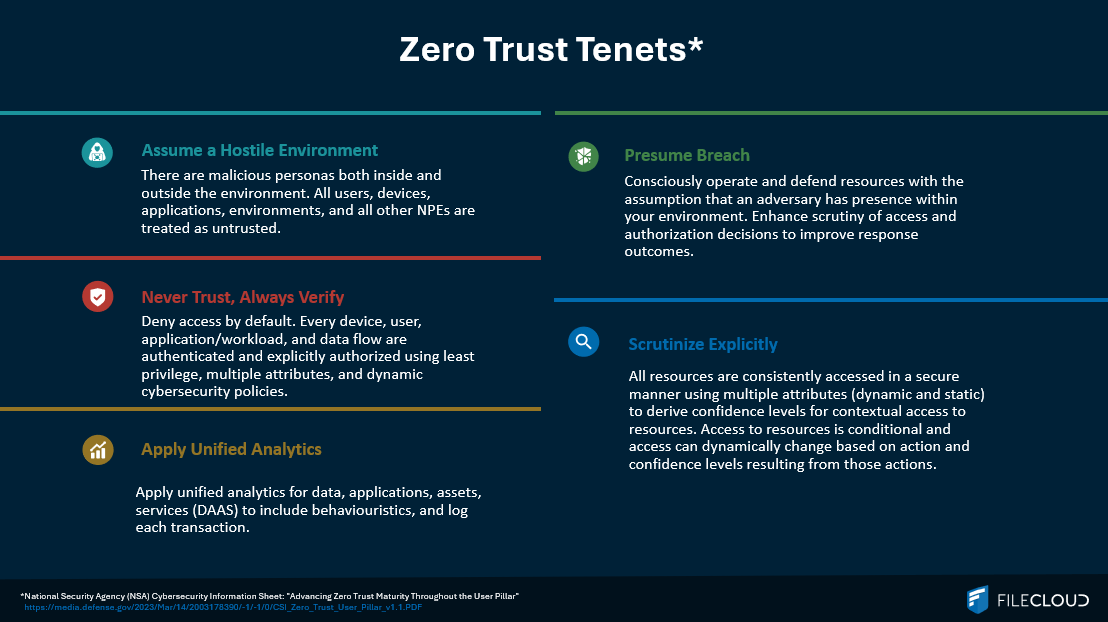
A modern DLP strategy should align with Zero Trust principles. Require continuous verification for users and devices, enforce least privilege access, and strictly control external collaboration.
Encrypt sensitive data beyond the network perimeter and assume no user or device is automatically trusted. Zero Trust strengthens DLP enforcement across distributed environments and remote workforces.
How FileCloud Supports a Modern, Scalable DLP Strategy
FileCloud provides the technical foundation required to support a comprehensive data loss prevention strategy. Organizations can enforce granular file and folder permissions, apply metadata-driven classification, and implement Zero Trust File Sharing® for secure external collaboration.
Built-in retention policies, audit-ready logging, and integration with DLP, SIEM, and identity systems support regulatory compliance and insider threat mitigation. Flexible deployment options including on-prem, hybrid, and regionally hosted environments help organizations address stricter data sovereignty requirements and maintain control over where sensitive data resides.
DLP Strategy and Implementation FAQs
What does a strong DLP implementation strategy include?
A strong DLP implementation strategy includes structured data discovery, classification controls, granular access enforcement, real-time monitoring, and automated policy execution. It should align directly with regulatory requirements and business risk priorities while integrating with identity management and security systems. Successful implementation also requires clear ownership, executive support, phased deployment, and measurable performance indicators to ensure long-term effectiveness.
What makes an effective DLP roll out strategy successful at scale?
An effective DLP roll out strategy succeeds when it prioritizes high-risk data first, applies clear classification standards, and introduces enforcement controls in controlled phases rather than all at once. Organizations that balance usability with security see higher adoption and fewer workarounds. Ongoing monitoring, policy refinement, and user education are critical to maintaining effectiveness as the environment evolves.
What should be included in a data loss prevention plan?
A comprehensive data loss prevention plan should clearly define sensitive data categories, document how data flows across systems and teams, establish access control policies, enforce encryption standards, and implement retention and deletion rules. It should also outline monitoring procedures, incident response protocols, and accountability structures. The plan must connect governance requirements with enforceable technical controls.
How should a DLP project be structured for enterprise environments?
A DLP project should begin with stakeholder alignment and risk assessment, followed by data discovery and classification. From there, organizations should design enforcement policies, test them in a pilot environment, and refine controls before scaling. Enterprise-level DLP projects require coordination between security, compliance, IT, and legal teams to ensure policies are enforceable and aligned with regulatory obligations.
What should a data loss prevention project plan include to support compliance?
A data loss prevention project plan must map each technical control to a specific regulatory or internal policy requirement. It should define how sensitive data is classified, how access is controlled, how retention is enforced, and how audit evidence is collected. This approach ensures compliance is built into the architecture rather than treated as a separate documentation exercise.
How does a data protection policy differ from a DLP strategy?
A data protection policy establishes the rules and expectations for handling sensitive information, while a DLP strategy enforces those rules through technology and process controls. The policy defines what should happen, and the DLP implementation strategy ensures it happens consistently through monitoring, classification, access restrictions, and automated enforcement.
How should cloud DLP be integrated into a broader security strategy?
Cloud DLP should operate as part of a unified security framework that includes endpoint protections, identity management, and access control systems. It must monitor data movement within cloud storage environments, enforce encryption, and restrict external sharing. For organizations operating in hybrid environments, cloud DLP must provide visibility and enforcement that align with on-prem systems to eliminate blind spots.
How does DLP support a broader data governance framework?
DLP supports a data governance framework by acting as the enforcement layer that ensures governance policies are consistently applied. Governance defines how data is categorized, stored, accessed, and retained. DLP ensures those rules are executed automatically through classification, monitoring, and access controls. Together, they provide structured oversight of sensitive data across departments, jurisdictions, and regulatory environments.

Product Marketing Manager