7 Secure Data Transfer Best Practices
Modern organizations move sensitive data across cloud platforms, endpoints, partners, and remote teams every day. Without a structured security framework, file sharing can quickly become a compliance risk and a breach vector. The following best practices help ensure data remains protected, traceable, and governed throughout its lifecycle.
1. Encrypt Data in Transit and at Rest
Encryption is the foundation of secure data transfer. Data should be encrypted while traveling across networks using secure protocols such as TLS, and encrypted at rest using strong standards such as AES 256. Encrypting data in transit prevents interception during transmission, while encrypting data at rest protects information even if storage systems are compromised. Together, these controls reduce breach impact and help organizations meet regulatory requirements.
Data At Rest vs In Data Transit: Encryption & Security Guide
Protecting Data At Rest vs Data In Transit: A Complete Guide to Data Encryption & Security Protecting data at rest and data in transit requires different security approaches because the data is in different states....
2. Adopt a Zero Trust Approach to File Sharing
A Zero Trust approach assumes no user or device should be trusted by default. Every access request must be verified, and permissions should follow the principle of least privilege. In practice, this means implementing time limited sharing links, password protection, strict read and write controls, and continuous identity verification. By limiting exposure and enforcing access boundaries, organizations reduce the likelihood of unauthorized access and contain potential damage if an incident occurs.
The Ultimate Guide to Zero Trust Implementation
Traditional perimeter-based security can no longer keep up with the growing cybersecurity threats and the shift to hybrid work. With employees, systems, and data now spread across multiple environments, trust must be continuously earned—not assumed....
3. Implement Granular Access Controls
Granular access controls ensure users only access the data necessary for their role. Role based permissions, group level controls, and segmentation between internal and external users prevent overexposure of sensitive files. Time bound access further reduces risk. This level of precision not only protects data but also strengthens compliance posture and simplifies audits.
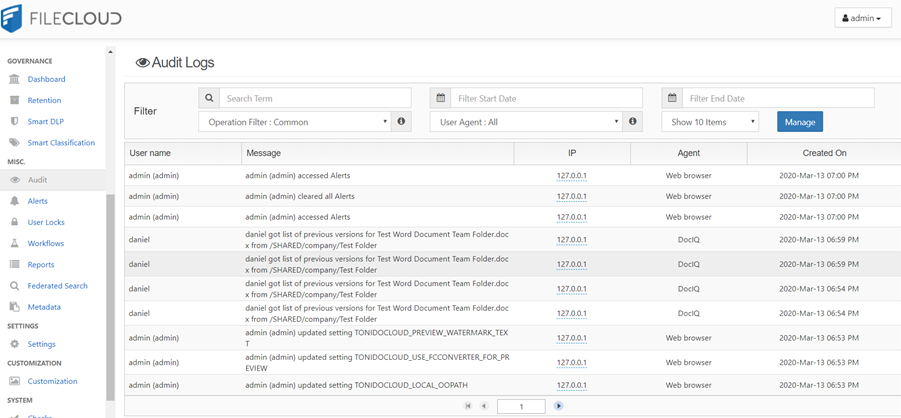
4. Enable Comprehensive Audit Trails and Monitoring
Visibility is critical to security. Comprehensive logging of uploads, downloads, edits, and sharing activities allows organizations to monitor behavior and detect anomalies. Real time alerts for suspicious activity and integration with SIEM systems support faster incident response. Detailed audit trails also provide documented evidence of compliance during regulatory reviews.
5. Automate Data Retention and Lifecycle Policies
Data should not be stored indefinitely without purpose. Automated data retention and lifecycle policies ensure files are archived, deleted, or moved according to regulatory and operational requirements. Automating these processes reduces human error, minimizes unnecessary data exposure, and supports data minimization strategies that are increasingly required by privacy regulations.
Data Retention Policy: 10 Best Practices
Data Retention Policy: 10 Best Practices In today’s data-driven world, organizations are generating and collecting information at an unprecedented rate. Effectively managing this data is not just an IT concern but a critical business imperative....
6. Secure External Collaboration with Controlled Access
External collaboration introduces additional risk if not properly managed. Secure portals, controlled guest accounts, password protected sharing, and expiring links help maintain control while enabling productivity. Organizations should ensure external users are subject to the same visibility and governance standards as internal users to prevent shadow IT and unmanaged file exchanges.
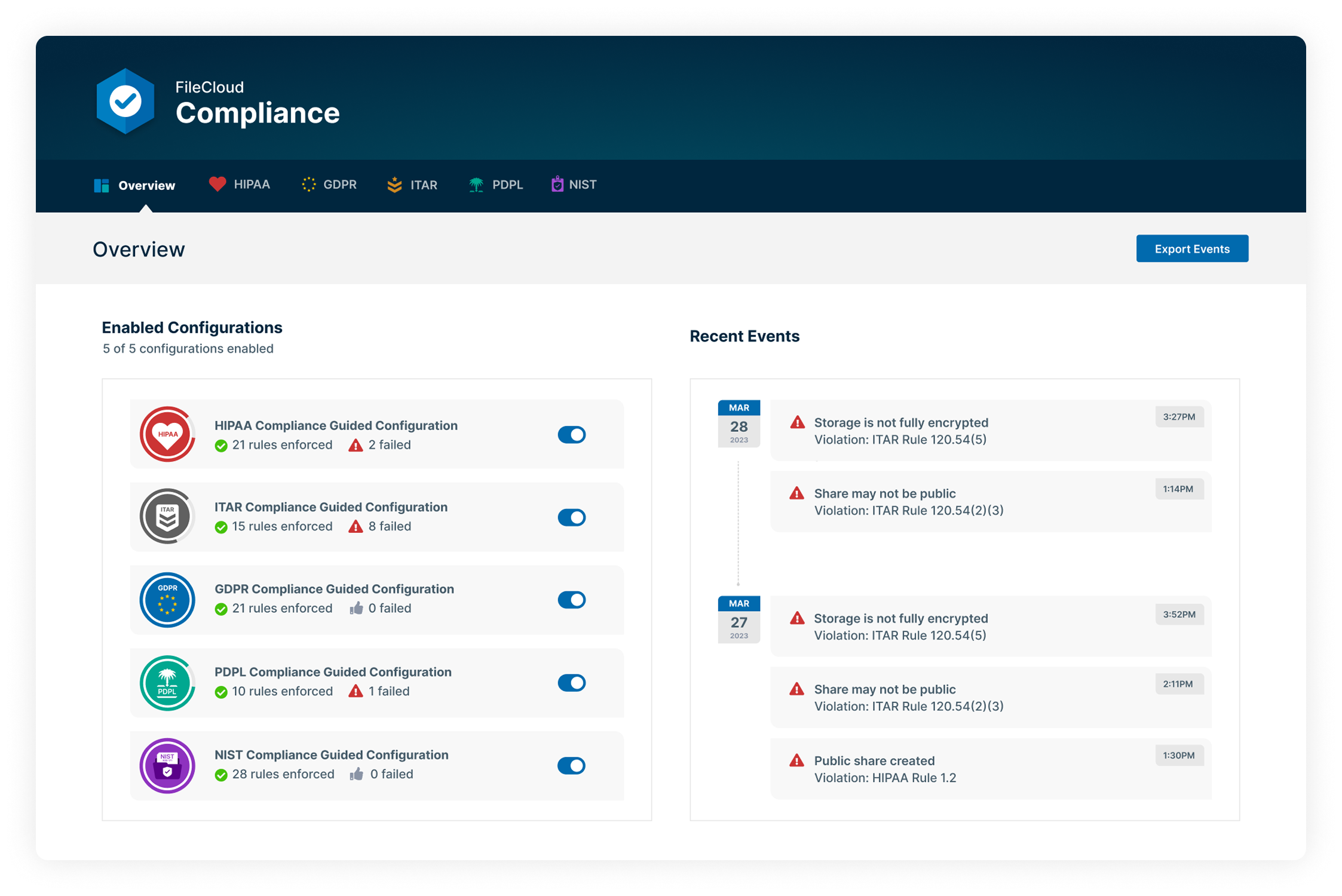
7. Centralize Governance and Compliance Enforcement
Security controls should not be fragmented across disconnected tools. Centralized governance allows organizations to enforce consistent policies, monitor activity in one place, and align file sharing practices with compliance mandates. Unified identity integration, consistent data loss prevention policies, and centralized reporting strengthen organizational control and reduce operational complexity.
Building a Secure Data Transfer Protocols
Secure data transfer requires a strategic approach that aligns technology, policy, and compliance. Organizations should follow a structured framework to reduce risk and strengthen governance:
- Evaluate current file sharing methods to identify security gaps and shadow IT usage
- Identify compliance gaps across regulatory frameworks such as GDPR, HIPAA, CMMC, or industry standards
- Map access control models to enforce least privilege and role based permissions
- Implement Zero Trust principles across internal and external collaboration workflows
Centralize monitoring and auditing to ensure full visibility into file activity
- Automate retention and governance policies to reduce long term exposure and administrative burden
This structured approach creates a scalable, defensible security posture that supports both operational efficiency and regulatory compliance.
How FileCloud Supports Secure Data Transfer Best Practices
Secure data transfer demands more than basic file sharing capabilities. It requires governance, visibility, and compliance built into the architecture. FileCloud supports these best practices through:
- Zero Trust File Sharing® capabilities that protect sensitive files with password protected encrypted archives.
- AES 256 encryption for data at rest and secure transmission protocols for data in transit
Granular access controls with role based permissions and controlled external sharing.
- Comprehensive audit trails and SIEM integration for full activity visibility and faster incident response.
- Automated retention policies to support lifecycle management and regulatory alignment
- On premises and regionally hosted deployment options to meet strict data residency requirements.
- Multi tenancy and white labeling to enable secure external collaboration while maintaining brand trust.
- Compliance ready architecture aligned with GDPR, HIPAA, CMMC, and other regulatory frameworks.
FileCloud is not simply file sharing. It is governed, secure, compliant data transfer designed for organizations that require control, transparency, and regulatory confidence.
FAQs: Secure Data Transfer
What are secure data transfer solutions?
Secure data transfer solutions are platforms or tools that protect sensitive information while it is being shared internally or externally. These solutions typically include encryption in transit and at rest, granular access controls, multi-factor authentication, audit logging, and compliance features to ensure data confidentiality and integrity.
What are the most important data transfer security standards?
Data transfer security standards vary by industry but commonly include encryption protocols such as TLS for data in transit and AES 256 for data at rest. Regulatory frameworks such as GDPR, HIPAA, CMMC, and ISO 27001 define requirements for protecting sensitive data during transfer. Many organizations also follow Zero Trust principles to enforce least privilege access and continuous identity verification.
What are healthcare data transfer security best practices?
Healthcare data transfer security best practices focus on protecting protected health information. Key measures include end to end encryption, strict role based access controls, detailed audit trails, secure file sharing portals, and automated data retention policies. Compliance with HIPAA and other regional privacy regulations is essential, along with full visibility into external data exchanges.
What are the most secure data transfer methods?
Secure data transfer methods include encrypted HTTPS connections, SFTP, managed file transfer platforms, and Zero Trust based file sharing solutions. The most secure approaches combine encryption, identity verification, time bound access, and comprehensive logging to ensure that only authorized users can send, receive, and access sensitive files.
What is secure data exchange?
Secure data exchange refers to the controlled sharing of information between individuals, organizations, or systems while maintaining confidentiality, integrity, and regulatory compliance. It involves encrypting data, verifying user identities, applying least privilege access controls, and maintaining visibility through monitoring and audit logs to reduce the risk of unauthorized access or data breaches.

Product Marketing Manager